How does cloud backup UK work?
Cloud backup is the process of protecting your organisation’s data by encrypting information and sending it over the internet to a secure offsite location.
Backing up to the cloud mitigates the risk of onsite threats like fire, flood, hardware issues, user error and, most commonly now – ransomware.
Once setup on your server or desktop, we can protect files, folders, databases and entire server images. Your data is encrypted with a key only you know and sent securely to our secure UK data centres.
This is performed automatically each day or as many times as you wish.
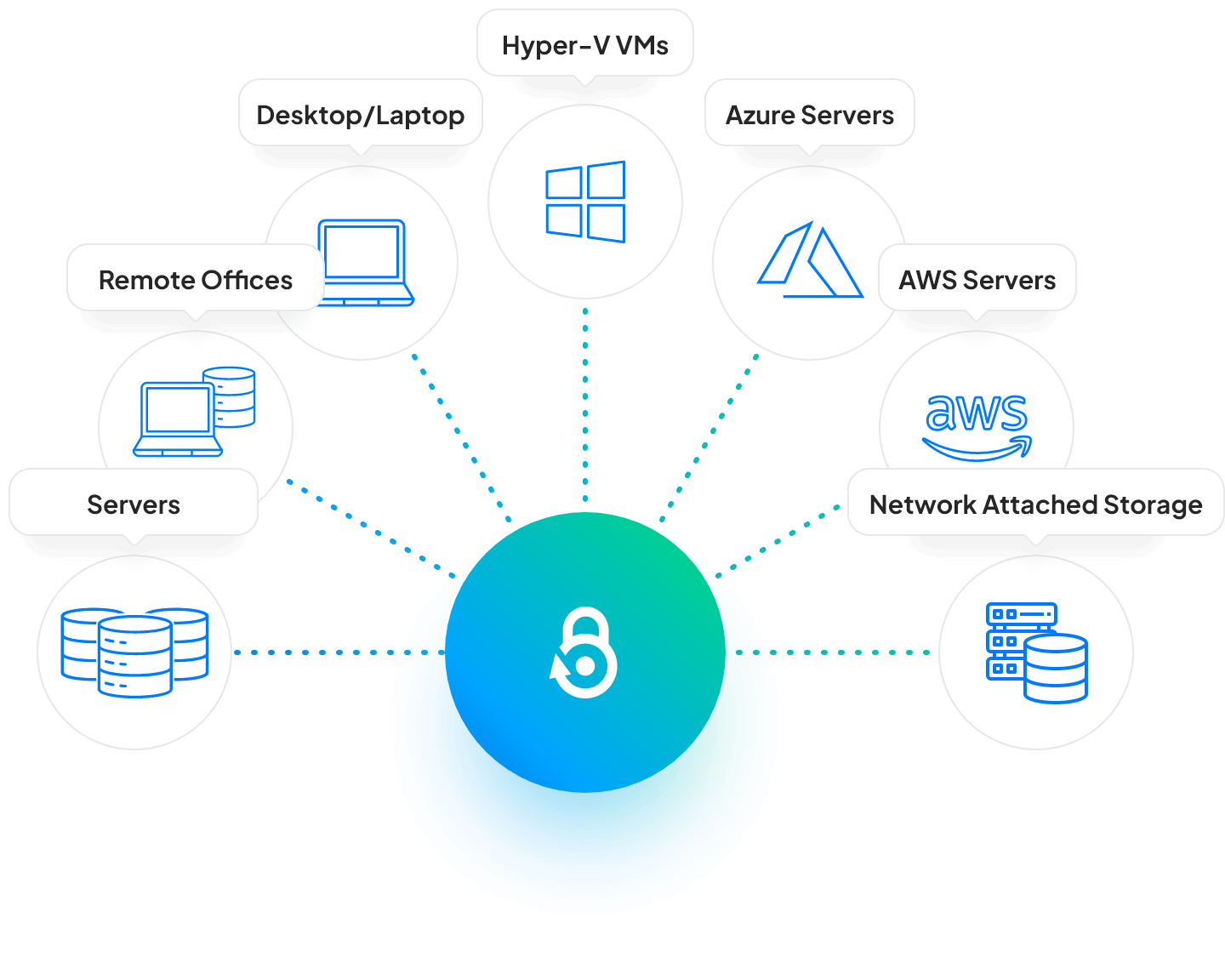
What sort of data can BackupVault protect?
The BackupVault cloud backup service can protect almost anything. Most common are simple files and folders, but we can also backup VSS-aware databases such as MS SQL and Exchange. Other databases and systems, such as MySQL and PostgreSQL, can also be protected.
VMWare and Hyper-V can be protected, and full server backups are supported to reduce recovery time significantly.
We are also able to provide specialist backup for schools, working with systems such as the Capita School Information Management System (SIMS).
Why Choose BackupVault
for Cloud Backup?
At BackupVault, we offer industry-leading cloud backup solutions designed to protect your critical data. Here’s why you should choose us for your cloud backup UK needs:
Data Upload Calculator
Would you like to know how long it will take to upload a backup to us? We have created the calculator below to help give an estimation of how long the transfer will take.
Note that the actual time taken may differ due to network overheads and how much the data compresses prior to transmission.
If you have a slow upload connection and/or a large amount of data, we are able to import the initial backup via our snapshot service. This is a free service and enables the initial backup to be sent to us via an encrypted USB disk.
Transfer Calculator
Total Transfer Time
0 days, 0 hours, 0 minutes, 4 seconds
Get a quote
Learn More About UK Cloud Backup
Cloud Backup: Protect Your Data Anytime, Anywhere
Automate the backup process and schedule regular backups to ensure continuous data protection without manual intervention.
Securely store your backups in off-site UK data centers equipped with robust security measures, protecting your data from physical disasters.
Version Control and Point-in-Time Recovery
Easily restore previous file versions or databases by leveraging version control and point-in-time recovery features.
Customise retention policies to align with regulatory compliance, legal obligations, and data management needs.
Hear From Our Clients
Common Online Cloud Backup Questions
Got further questions about cloud backups? Don’t hesitate to reach out and ask us.
It’s secure, completely automatic and offsite. It is also easy to use and requires very little user intervention. You will never again need to remember to change tapes or disks – everything “just works”.
As the UK backup service is completely managed we will do all the hard work for you. We also offer 24-hour telephone and email support as standard which one of the many reasons our customers choose BackupVault.
At BackupVault we take your privacy and security very seriously. With our secure online backup solution, your data is encrypted on your PC/server with the encryption key known only to you. The encrypted data is transferred over the Internet to our secure servers where it remains encrypted ready for rapid restoration. Our datacentres are also state of the art with numerous physical security measures in place.
Online backup pricing can vary widely depending on the provider, your requirements and how software providers structure fees for their services.
As well as checking what’s included in the price, it’s important to consider how efficient the service is as you may find the backup storage you thought you paid for exceeds the agreed capacity very quickly. Our business cloud backup starts from as little as £20 per month. The price you pay depends on your data storage requirements.
This is often much less than you think, so we highly recommend speaking to us for an accurate quote.
To use cloud backup, you need to install our backup client on a laptop, desktop or server. You can then select which data you want to backup to the cloud and how often. Once this has been set up your backup will run automatically in the background. It’s a set and forget user experience – until you need it.
Your backup files can be accessed in several ways. The most common route is to open the backup client software, select Restore, then pick a date and the files/folders to restore.
You can also mount a virtual drive on any PC and restore data from there.
Free Trial
Backup your critical business data on the cloud with enterprise-level UK support.