The Great Shift: Attackers Move from Email to Teams; and AI is Leading the Charge
Written By:

Rob Stevenson
Founder
Based on insights from the Acronis Cyberthreats Report, H1 2025, reviewed by BackupVault.
The Message That Looked Completely Ordinary
A Microsoft Teams message arrives from “Finance”. A OneDrive file is shared by “Operations”. A Slack message asks for urgent approval.
Everything looks normal. These are the tools small businesses use every day to stay productive, collaborate quickly, and avoid unnecessary friction.
Minutes later, however, the warning signs appear:
OAuth alerts (signs that an app or service has been granted access to an account). Suspicious token exchanges (digital “keys” being passed around without approval). Impossible-travel login attempts (logins from locations the user could not physically reach in time). New inbox rules you did not create. External connections you never approved.
The malicious attack did not come through email. It came through collaboration tools. This is the new cyber reality, and smaller organisations are firmly in the crosshairs.
Chapter 1: Why Email Is No Longer the Primary Attack Surface
1. Email defences have significantly improved
Email has been the main target for cybercriminals for decades, and even small and medium businesses now benefit from stronger default protections.
In the past year:
- Malicious email dropped from 1.5% to 1.1%.
- The total number of malicious attacks per organisation fell from 291 to 205.
Spam filtering, link scanning, and basic user awareness training are now commonplace. Email is no longer the easiest way in. Attackers adapted.
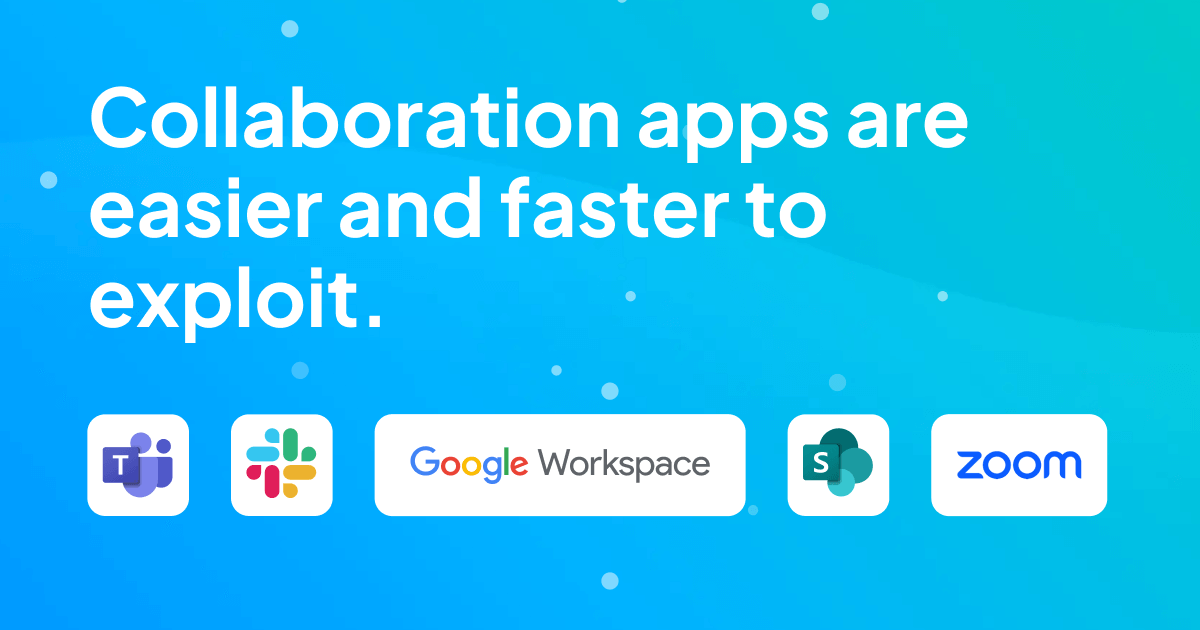
2. Collaboration apps are easier, faster, and cheaper to exploit
Platforms such as:
- Microsoft Teams
- Slack
- Google Workspace
- SharePoint
- Zoom Chat
These tools are essential for small teams. They are trusted, informal, and built for speed. Messages feel internal. Files feel safe. Urgency feels normal.
That trust is exactly what attackers exploit.
As a result:
- Phishing through collaboration apps jumped from 9% to 30.5%.
- Advanced attacks rose from 9 per cent to 24.5%.
These attacks do not require elite skills or expensive tooling. Many are launched using readily available phishing kits, compromised accounts, or basic automation. Smaller businesses are attractive targets precisely because defences are lighter and trust is higher.
Chapter 2: 2025’s Major Cyber Campaigns (What This Means for Smaller Businesses)
1. Mass-Scale Phishing Is Now Accessible to Anyone
Large phishing campaigns no longer require large criminal organisations. Pre-built templates, automation tools, and rented infrastructure mean almost anyone can launch convincing attacks.
For small businesses, this means attackers do not need to “target” you specifically. They only need one person to click.
IT manager insight: You are not too small to be targeted. You are simply easier to reach.
2. Malware Hidden in Everyday Files
Modern malware is commonly delivered through files that look routine, such as invoices, shared documents, or password-protected downloads.
- Once installed, the malware can:
- Record keystrokes.
- Capture screenshots.
- Steal files quietly in the background.
Why this matters: smaller organisations often rely on informal processes and trust-based file sharing. Attacks are designed to blend in, not break systems immediately.
3. Smishing and Mobile-Based Attacks
Attackers increasingly use SMS and messaging apps instead of email.
Millions of clicks and hundreds of thousands of stolen payment details came from campaigns that bypassed traditional spam controls entirely.
For small teams, where personal and work devices often overlap, mobile phones are now a direct entry point into the business.
IT manager insight: If it connects to business systems, it is part of the attack surface.
4. Impersonation and Trust Abuse
Attackers frequently pose as suppliers, service providers, or recruiters. These scams do not rely on deepfake technology or advanced techniques. They rely on familiarity, urgency, and routine interactions.
One compromised account in a small business can expose everything.
Chapter 3: Why Collaboration Tools Are the Weakest Link for SMEs
Several factors make collaboration platforms especially vulnerable in smaller environments:
- Implicit trust between users.
- OAuth tokens that provide long-term access without passwords.
- Third-party apps added for convenience, not security.
- No equivalent of email protections for chat messages.
- Real-time communication that discourages verification.
Collaboration tools were designed to remove friction. Attackers take advantage of that design.
Chapter 4: What IT Managers Must Do Now
1. Gain visibility across cloud platforms
Small IT teams cannot protect what they cannot see. Security tools must show:
- Which apps have access to user accounts.
- External connections into the environment.
- Unusual file sharing or login behaviour.
Visibility is the foundation of security.
2. Treat chat like email
If users receive links, files, and requests through chat tools, those tools must be protected accordingly:
- Links scanned before clicks.
- Attachments analysed safely.
- Clear warnings for external contacts.
The delivery method has changed. The risk has not.
3. Secure and scan backups
Backups often contain phishing links and malicious attachments.
For smaller businesses, backups are critical. Restoring infected data can undo recovery efforts instantly if threats are not detected first.
4. Strengthen identity and access controls
Security must account for context, not just credentials:
- Conditional access rules.
- Trusted devices.
- Alerts for unusual behaviour.
- Detection of impossible-travel logins.
This reduces risk without slowing teams down.
Conclusion: Small Businesses Are No Longer Off the Radar
Cyber threats are no longer reserved for large enterprises. Teams, Slack, Google Drive, and SharePoint are now common attack paths precisely because smaller organisations rely on them heavily and protect them lightly.
The question is no longer: “Are we big enough to be targeted?”
It is: “Are we easy enough to compromise?”
The attack landscape has shifted, and small and medium businesses are now a valid, valuable target. Defending against this reality alone can overwhelm limited time, skills, and resources.
BackupVault helps SMEs secure their entire communication ecosystem. With 24/7 UK support and a practical, consultative approach, we help you reduce risk without adding complexity.
Get in touch today and let us help you strengthen your collaboration security strategy.